Email authentication is one of the technical aspects of the marketing world that most people only “kind of” understand.
The email authentication process can be puzzling at best and downright scary at worst for marketers. Today, we will try to simplify things for you so that next time someone brings up DKIM, SPF, or DMARC – your first instinct won’t be to hide in a corner.
So, let’s get started!
Most types of transactions require authentication. Whether you’re a patient seeking treatment, a motorist seeking a license, or anyone else, you must authenticate and prove your identity before proceeding with the process.
And the same is true for email deliverability. In the Internet world, you must prove that you are an authenticated sender to get past ISP (Internet Service Provider) filters.
SPF, DKIM, and DMARC are terms for server authentication and validate that the sender has the authorization to send emails. These three terms establish that a sender is a real person who has been sending emails from their domain rather than impersonating someone else.
As with growing frauds in the Internet world, all email systems have become more selective and strict regarding the types of emails they accept.
Having SPF, DKIM, and DMARC enabled will ensure that emails are being sent as needed rather than being rejected.
So what exactly are SPFD, DKIM, and DMARC?
What does SPF mean?

SPF, or Sender Policy Framework, is an email validation system that detects and blocks any kind of email spoofing. It allows mail exchangers to check that incoming mail from a particular domain is originated from a specific IP address.
An SPF record is a TXT record in the Domain Name System (DNS) that specifies which IP addresses and servers can send email “from” that domain.
After the message has been sent, ISPs examine the Return-Path domain. The next step is to determine whether or not the IP address used to send the email matches the IP address given in the Return-Path domain’s SPF record. In this situation, the message will be delivered once SPF authentication has been verified.
Let’s understand this better with an example Here’s how an SPF record’s basic components looks like:
Here is an example of the core components of an SPF record:
v=spf1 ip4=142.0.2.0 ip4=142.0.2.1 include:IPPC@gmail.com -all
Let’s break down the individual components to understand how it works:
- “v=spf1” indicates to the server that this file has an SPF record. This string must appear at the start of every SPF record.
- The SPF record tells the server that ip4=142.0.2.0 and ip4=142.0.2.1 are authorized to send emails on behalf of the domain in this case. It is often referred as “guest list,”.
- “Include: IPPC@gmail.com”, this “include” tag indicates that the added domain’s SPF record content is valid & which tells the server which third-party organizations are authorized to send emails on behalf of the domain
- Finally, -all informs the server that any address not mentioned in the SPF record is not authorized to send emails and should be denied.
What is the importance of SPF?
SPF (Sender Policy Framework) is a suggested standard for protecting email subscribers from spammers because fake sender addresses and domains are pretty common in email spam and phishing.
This is why posting and verifying SPF data is regarded as one of the most dependable and easy anti-spam tactics.
A spammer may attempt to send an email from your domain in order to take advantage of your good sender reputation. However, if correctly set, SPF authentication will tell the receiving ISP that the transmitting server does not have the authorization to send an email for your domain while the domain is yours.
SPF notifies incoming mail servers that a message was delivered from a domain that has been authorized by the domain mentioned.
What is DKIM?
DKIM stands for Domain Keys Identified Mail, an email authentication system that allows the recipient to confirm that an email was sent and approved by the domain’s owner.
This is done by adding a digital signature to the email, and then the DKIM signature is embedded in the message as an encryption-protected header.
When a receiver (or receiving system) detects an email with a valid DKIM signature, it knows that the email’s components, such as the message body and attachments, haven’t been manipulated.
Because DKIM signatures are validated on the server, they usually are not accessible to end-users. Using the DKIM standard will enhance the email deliverability rate even more if you combine it with DMARC and SPF data.
DKIM is a TXT record signature that assists both the sender and the receiver in establishing trust.
What is the significance of DKIM?

DKIM protects recipients from any kind of phishing attacks and prevents spammers from committing fraudulent activities. As a result, your email delivery improves, and stakeholder trust develops.
Let us try to understand this better with an example: a retailer is launching an email campaign to advertise a new product line. Messages flagged as spam or not delivered to intended recipients will not be distributed until it’s verified, causing the firm to lose business.
Spammers can take advantage of such an opportunity to tailor their phishing emails relating to the campaign, increasing the likelihood of customers becoming confused and victims of such frauds.
DKIM is used in email delivery to establish that:
- The content of an email has not been tampered with.
- The email headers haven’t changed since the original sender sent them.
- The email’s sender owns or authorizes the domain’s owner to use the DKIM domain.
DKIM is a digitally encrypted signature that can be used to “sign” an email message. This signature appears as a header in an email message.
For example, suppose someone sends an email claiming to be from Facebook.com. In that case, the subscriber’s incoming mail server can check Facebook’s digitally-encrypted signature to see if it came from their server or not. If you don’t, your mail will be blocked or not delivered.
(Note* The header will show whether or not the DKIM signature is authentic.)
A DKIM record is actually a DNS TXT (“text”) record. Any text that a domain administrator wants to associate with their domain can be stored in TXT records. This sort of DNS record has several applications, including DKIM.
A DKIM DNS TXT record looks like this:
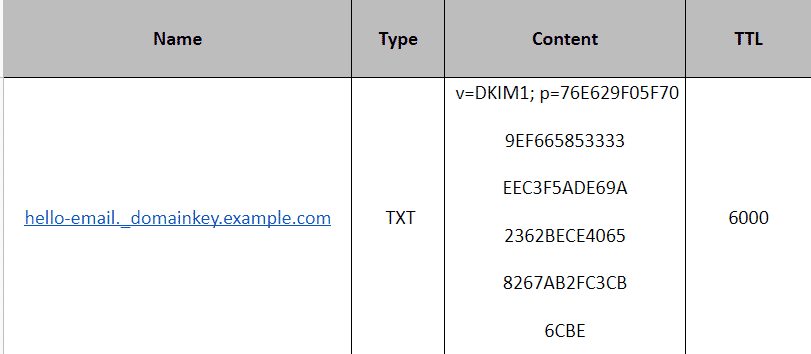
DKIM records, unlike other DNS TXT records, are stored under a unique name rather than the domain name. The following is the format for DKIM record names:
[selector]. domainkey.[domain]
The selector is a customized value supplied by the domain’s email service provider. It’s included in the DKIM header to allow an email server to do the necessary DNS lookup for DKIM. The domain is the email domain name. ._domainkey. is included in all DKIM record names.
Email servers employ the DKIM selector provided by the email service provider to look for the DKIM record, & not just the domain name.
Assume that example.com’s email service provider is ‘Hello Email’, and it utilizes the DKIM selector ‘hello-email’. Although the majority of example.com’s DNS entries are named example.com, their DKIM DNS record is marked hello-email.domainkey.example.com, as shown in the example above.
What exactly is DMARC?

DMARC, or Domain-based Message Authentication, Reporting, and Conformance is a framework that uses the Sender Policy Framework (SPF) and DKIM to determine the validity of an email message.
Internet Service Providers can utilize DMARC records to avoid malicious email practices such as domain spoofing and phishing for recipients’ personal information.
In essence, it allows email senders to choose how to handle emails that haven’t been certified with SPF or DKIM. Senders can direct those emails to the spam folder or have them blocklisted entirely.
ISPs can use DMARC to detect spammers better and prevent malicious emails from reaching consumers’ inboxes. This can help eliminate false alerts, improve authentication, and increase transparency in email deliverability processes.
When creating a DMARC record, you can select one of three policies. These policies educate the receiving server on how to treat your non-DMARC-compliant email.
- None: Treat all mail from your domain as if DMARC hadn’t validated it.
- Quarantine: The receiving server accepts the message, but it will be delivered to another location, usually the spam folder rather than the recipient’s inbox.
- Reject: The message is entirely rejected.
DMARC is based on SPF and DKIM, and it ensures that the information in both records matches the domain server when an email is received. This is also known as identifier alignment at a time.
Continuing the above example: When someone sends an email claiming to be from Facebook.com, the subscriber’s receiving mail server checks to determine if both SPF and DKIM protect the message. If neither authentication method works, it alerts the receiving mail server on what to do.
How are SPF, DKIM, and DMARC related?
Email authentication technologies such as DKIM, SPF, and DMARC all help with different parts of the process.
SPF: Senders can use SPF to specify which IP addresses are permitted to send an email for a specific domain.
DKIM: It provides an encryption key as well as a digital signature to confirm that an email message has not been tampered with or forged.
DMARC: This framework combines the SPF and DKIM authentication protocols into a single framework, allowing domain owners to determine how an email should be handled if an authorization test fails.

